Compliant VDI is a purpose-built solution from First Column IT that enables your business to rapidly achieve CMMC Level 2 certification with end-to-end audit support, without requiring migration of your existing infrastructure. The platform is designed to reduce the total cost and complexity of achieving compliance for small and mid-sized businesses.
Compliant VDI is a complete CMMC Level 2 solution that includes environment deployment, ongoing management, policy and procedure development, compliance consulting, audit preparation, and coordination with trusted C3PAO assessors. The platform is designed to support organizations handling Controlled Unclassified Information (CUI) within a secure, centralized environment aligned to NIST SP 800-171, DFARS 252.204-7012, DFARS 252.204-7021, and Microsoft 365 GCC High requirements.
Organizations gain a controlled, cloud-hosted workspace that reduces risk, limits compliance scope, and simplifies audit readiness. This enclave model is especially effective for organizations with limited CUI workflows that do not require mobile device access or integration with local peripherals such as printers or USB removable media.This approach is well suited for teams who require secure access to CUI within a clearly defined and isolated compliance boundary.
Compliant VDI is built for streamlined and predictable audits, with security controls aligned to CMMC Level 2 and NIST 800-171 from day one. The environment enforces access control, audit logging, encryption, and boundary protection within a Microsoft 365 GCC High environment aligned with DFARS requirements.
First Column IT provides integrated audit support, including evidence collection, policy creation, control validation, audit preparation, and direct engagement with assessors. This structured and repeatable approach reduces internal workloads while ensuring organizations are fully prepared to demonstrate compliance during formal CMMC assessments.
Compliant VDI delivers secure remote desktop access through a Zero Trust architecture, ensuring that CUI remains within the protected enclave and is never stored on local endpoints. Users can securely access the environment from approved devices while maintaining strict data protection controls.
Designed specifically for defense contractors and organizations supporting federal contracts, Compliant VDI enables secure collaboration and access while maintaining alignment with CMMC, DFARS, and federal cybersecurity requirements.
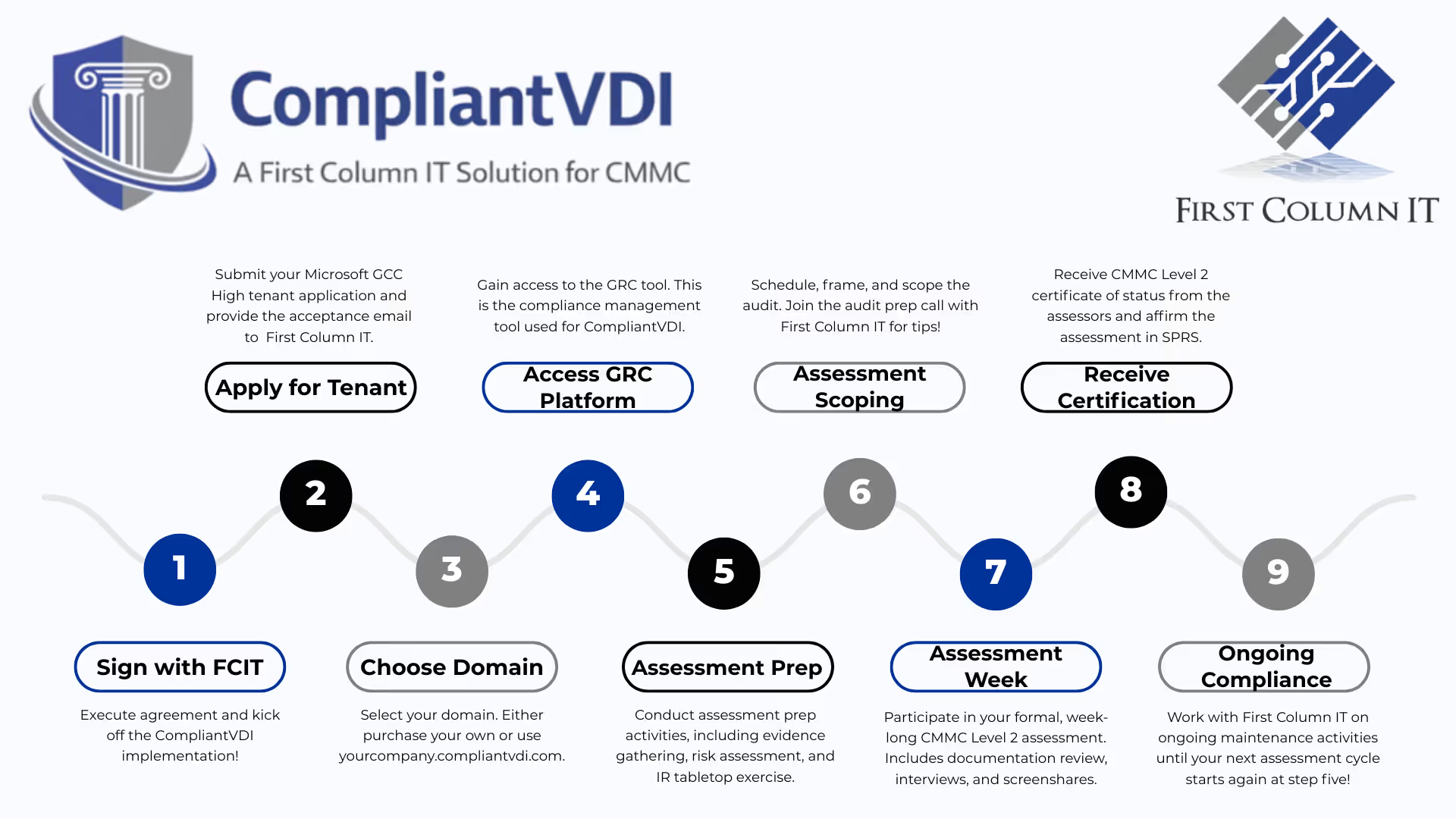
Compliant VDI follows a structured and repeatable implementation model designed to help organizations efficiently prepare for a CMMC Level 2 assessment in as little as 90 days.
First Column IT builds and configures the secure CMMC enclave within a GCC High environment, establishes system boundaries, and prepares the compliance platform. During this phase, policies and procedures are developed and approved, and the environment is prepared for secure deployment and audit readiness.
First Column IT works with trusted C3PAO assessors to define audit scope, coordinate scheduling, and prepare for assessment. Organizations are guided through evidence collection for both technical and organizational controls, including areas such as personnel security and administrative processes. All required artifacts are aligned with CMMC Level 2 requirements using a structured and repeatable methodology.
During the formal audit, First Column IT actively supports assessment sessions, leads technical discussions, and facilitates auditor walkthroughs. This reduces the burden on internal teams and ensures a consistent and well-prepared audit experience.
While no provider can guarantee certification outcomes, First Column IT has achieved a 100% certification success rate for organizations that have completed CMMC Level 2 assessments using the Compliant VDI platform.
ADVANCE YOUR BUSINESS

Although compliance is there to protect you and your clients, it can be catastrophic should you ever fail to be compliant with your regulatory body. Our team of compliance experts is fluent in the latest requirements in CMMC, NIST, HIPAA, PCI-DSS, FINRA, GDPR, DFAR, SOX, and more.

Without your data, how would you operate your business? We protect your data with non-disruptive backups to multiple locations and ensure that you and your team have a plan in place should a disaster take your business offline for any reason.

We go beyond the basics of firewall, anti-virus and intrusion prevention services (IPS) to ensure you have multiple layers of zero trust ongoing protection beyond what most of our competitors provide. Because if your security offers only a single point of protection, you’re more vulnerable to breaches – and that just doesn’t work for us.

The password - as an adequate security measure - is long dead. In 2022, about 30,000 websites are hacked each day and 64% of companies worldwide have suffered at least one form of a cyber-attack. Two Factor (2FA) deployed for all entry points including workstations, terminal servers, Office 365, and VPN is critical to protecting your valuable data!